Nozomi Networks’ industrial cybersecurity solutions are designed to protect mission-critical environments across all industries and sectors, including today’s OT and IoT physical devices and processes. We deliver:
- Unmatched protocol coverage and comprehensive, accurate analysis of dozens of OT, IoT and IT protocols
- AI-driven insights and root cause analysis provide actionable intelligence to accelerate response or guide remediation efforts
- Proven in the largest and most complex customer environments around the world
- Unique ability to write ad hoc queries to create alerts when assets or systems are not functioning correctly
- Seamless integration with SIEM and SOC systems for closing operational visibility and security gaps
- Rigorous forensic analysis for incident response and greater insights
- Global partner ecosystem for purchasing and service needs
Anticipate
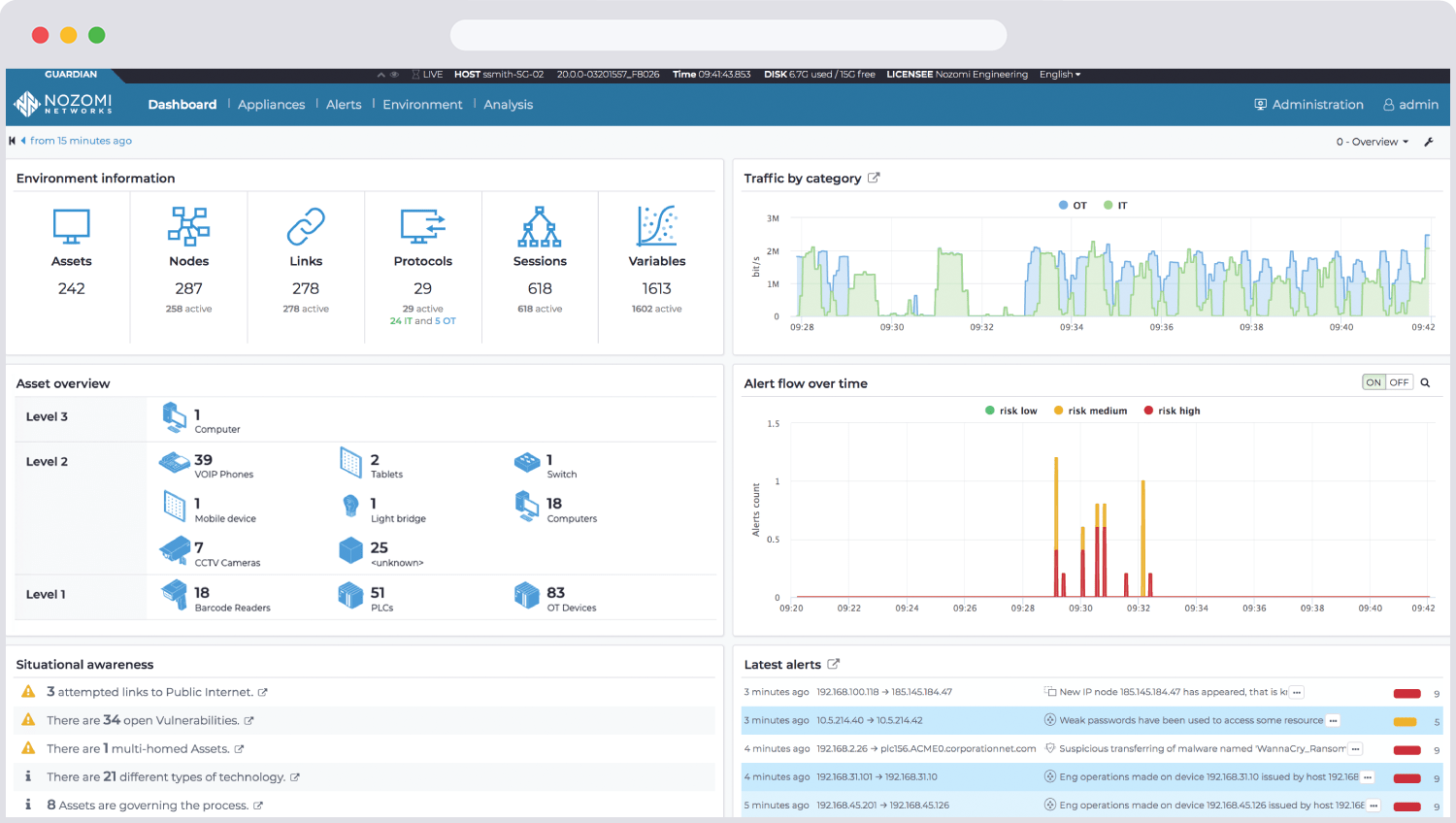
Unparalleled OT and IoT visibility helps you foresee potential security and reliability threats long before they impact operations.
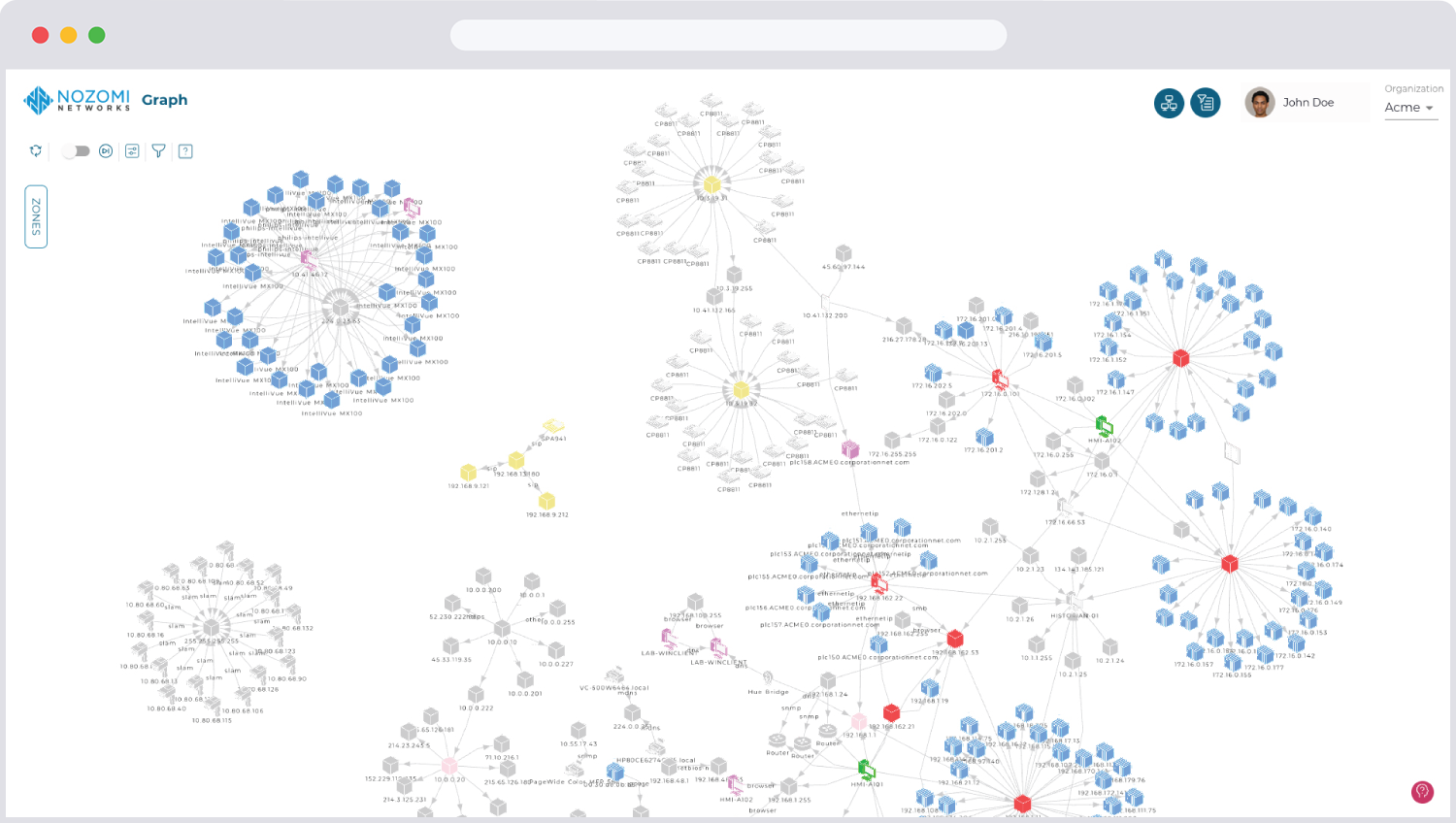
Figure 1 - Network view provides an interactive vizualization of your network.
Key Platform Features
Network Visualization
Get a complete view of communicating devices and traffic patterns to build a visualization map that can accelerate research and quickly identify anomalies and incidents.
Workbooks
Workbooks prioritize remediation efforts by highlighting the most critical endpoint vulnerabilities.
The first phase of cybersecurity maturity is understanding what is on your network and anticipating where risks may arise.
Nozomi Networks provides visibility to all your endpoints with deep data collection that can expose vulnerabilities and highlight where to focus risk management efforts. Visualize your device connections and traffic patterns to facilitate research and compliance efforts. Anticipate security threats before they impact your operations, while reducing risk and compliance efforts.

 http://www.globalsafe.com.cn/8b792bbf-f601-4a3f-9cf9-5a7bd8125284">
http://www.globalsafe.com.cn/8b792bbf-f601-4a3f-9cf9-5a7bd8125284">
Quickly detect and respond to cyber threats, risks, and anomalies with a scalable SaaS platform that consolidates IoT and OT security management into a single application.
- Asset Discovery & Network Visualization
Eliminate blind spots and increase your cyber threat awareness.
Automatically track your OT, ICS, and IoT/IIoT devices in an up-to-date, accurate asset inventory- Drill down from macro view for detailed information on endpoints and connections

-
Immediately see your entire OT network.
- Visualization of all devices on your network
- Extensive node information including name, type, and firmware version
- Actionable insights into asset behavior, roles, protocols, data flows and more

Network Visualization View displays all assets communicating on your network for real-time awareness.
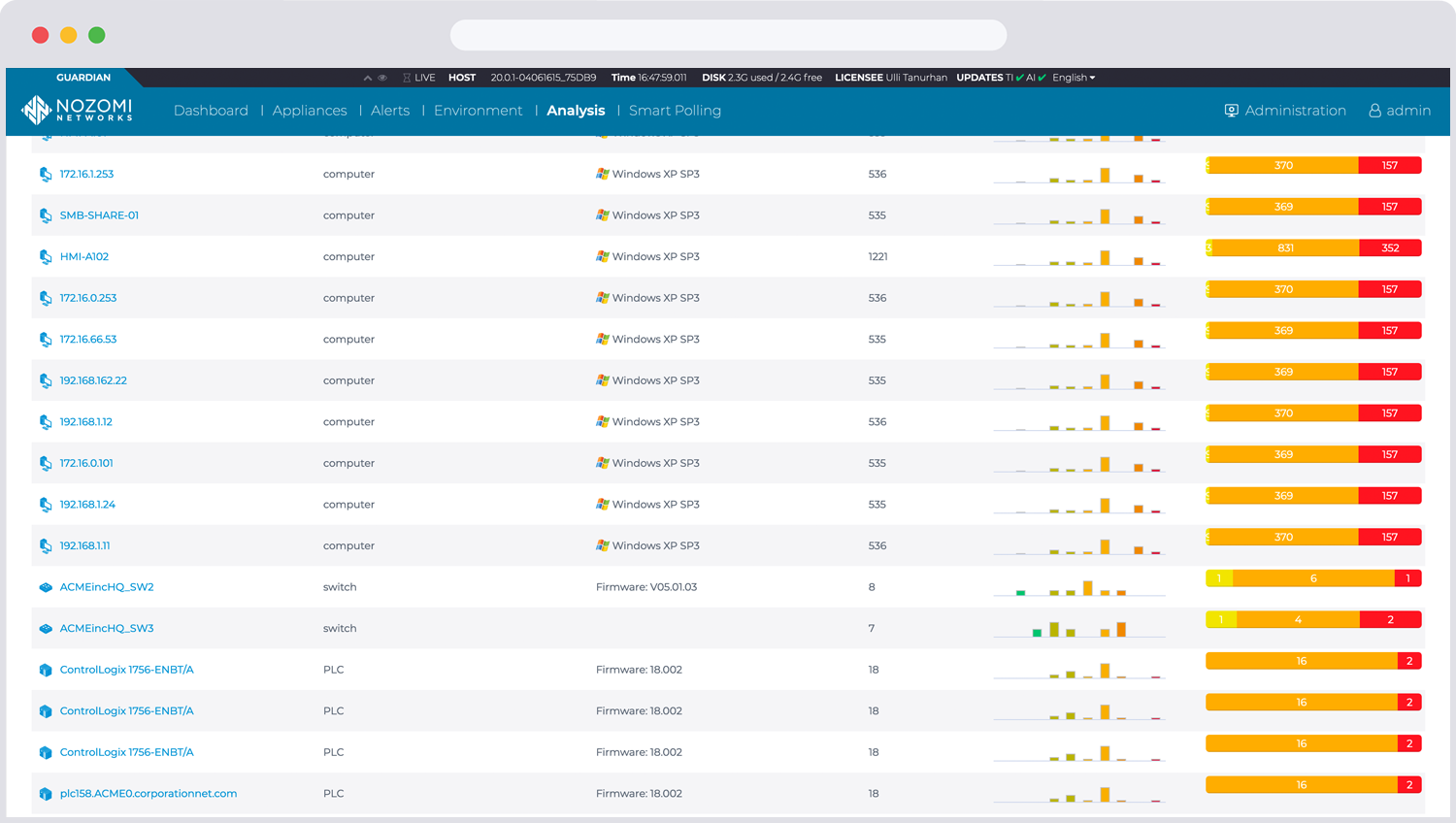
IoT & OT Vulnerability Management
Rapidly identify OT/IoT network risks, assess vulnerabilities and prioritize response.
- Detailed risk information including security alerts, missing patches and vulnerabilities
- Automated vulnerability assessment
- Efficient threat prioritization and remediation
Continuously monitor your networks and automation systems.
- Eliminate blind spots caused by limited monitoring or inadequate protocol support
- Easy access to detailed OT, ICS and IoT/IIoT cyber risk data
- Highlights potential reliability issues, such as unusual process values